about
Hi, I'm Bhushan Nandita Anand Ladgaonkar. I am a Computer Engineering student at Fr. Conceição Rodrigues College focused on offensive security operations and machine learning. I independently pursue advanced knowledge from sources like CS50 and pwn.college to deepen my expertise, with the goal of creating robust, secure digital experiences.
experience
Internship @ ONGC
Summer Intern | Database Group (WOB)
Developed an ML-based Network Intrusion Detection System (NIDS) to address the limitations of static signature-based security. Engineered a data pipeline processing the UNSW-NB15 dataset (2M+ records) and optimized detection models (RandomForest, XGBoost) using SMOTE to handle class imbalance. Analyzed zero-day attack patterns under the guidance of the Database Programming division.
skills
> Languages
- Python
- C / C++
- Java
- SQL
> Security
- Kali Linux
- Burp Suite
- OSINT
- Cyber Kill Chain
- Recon & Enumeration
> Data & ML
- Pandas
- NumPy
- Scikit-learn
- Machine Learning
projects
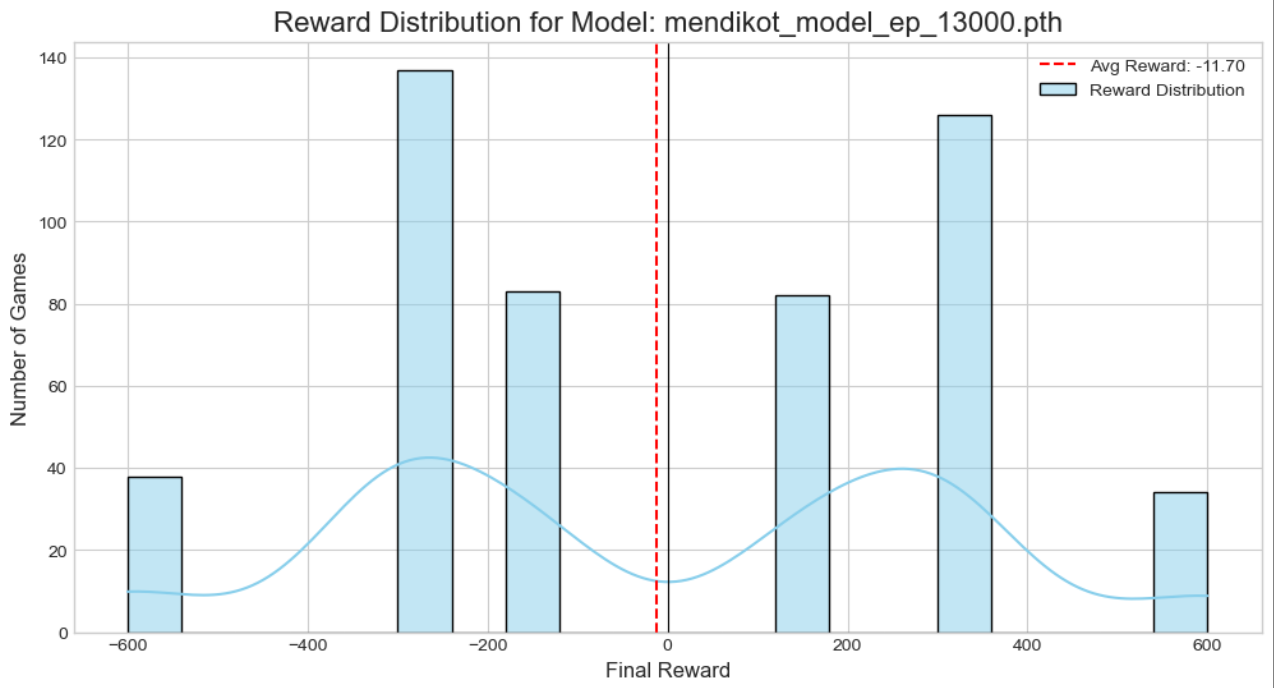
MendikotZero: AlphaZero RL Agent
Engineered an autonomous AI agent for the Indian card game 'Mendikot' using Deep Reinforcement Learning. Implemented the AlphaZero architecture from scratch, utilizing Monte Carlo Tree Search (MCTS) guided by a Dual-Head Neural Network. The agent was trained via self-play without human data, evolving from random moves to advanced strategic planning.
View Code & Paper
CS50 Introduction to Cybersecurity: Final Project
Anatomy of a Critical Failure : CVE-2025-61882
CS50 Cybersecurity Capstone: Conducted a technical forensic analysis of a critical (CVSS 9.8) Path Traversal vulnerability in Oracle Agile PLM. Deconstructed the input validation failure and proposed defense-in-depth remediation strategies including Path Canonicalization and Least Privilege architecture.
Watch Analysis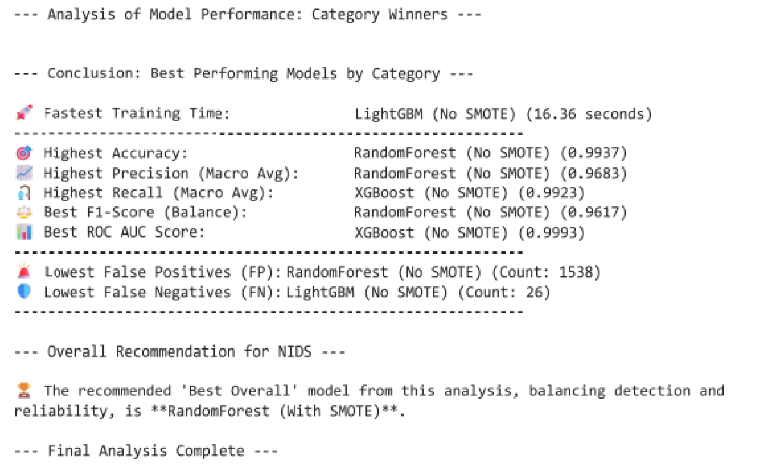
Network Intrusion Detection System
Developed a high-performance NIDS using machine learning to detect novel and zero-day attacks. Executed a full data science workflow on the UNSW-NB15 dataset. The final Random Forest model (with SMOTE) achieved an excellent balance between high detection rates and low false positives.
View on GitHubcertifications
CS50 Cybersecurity (Harvard)
Cyber Kill Chain
OSINT
Offensive Security Ops
Recon & Enumeration